Bgp hijacking bitcoin wallet
Routing Attacks on Cryptocurrencies to appear at the IEEE Symposium on Security and Privacy, we shed light on these aspects by studying the security of Bitcoin from an Internet routing perspective and quantify the potential disruptive effects of network attackers.
Among others, we show that:. In this post, we take a closer look at these issues. We start by describing the two possible network attacks which we consider, namely partitioning and delay attacks, along with their potential impact on Bitcoin. We then discuss some short and long-term countermeasures that would increase Bitcoin's robustness against network attackers. More details on our work can be found on our website. With partitioning attacks, an attacker aims at splitting the Bitcoin network into at least two disjoint components such that no information e.
To partition the network into two components, a network attacker intercepts all the traffic destined to all the Bitcoin nodes contained within one of the component and drops any connection to the other component. To intercept traffic, a network attacker relies on vulnerabilities in the Border Gateway Protocol BGP , the only Internet routing protocol used today, which does not validate the origin of routing announcements.
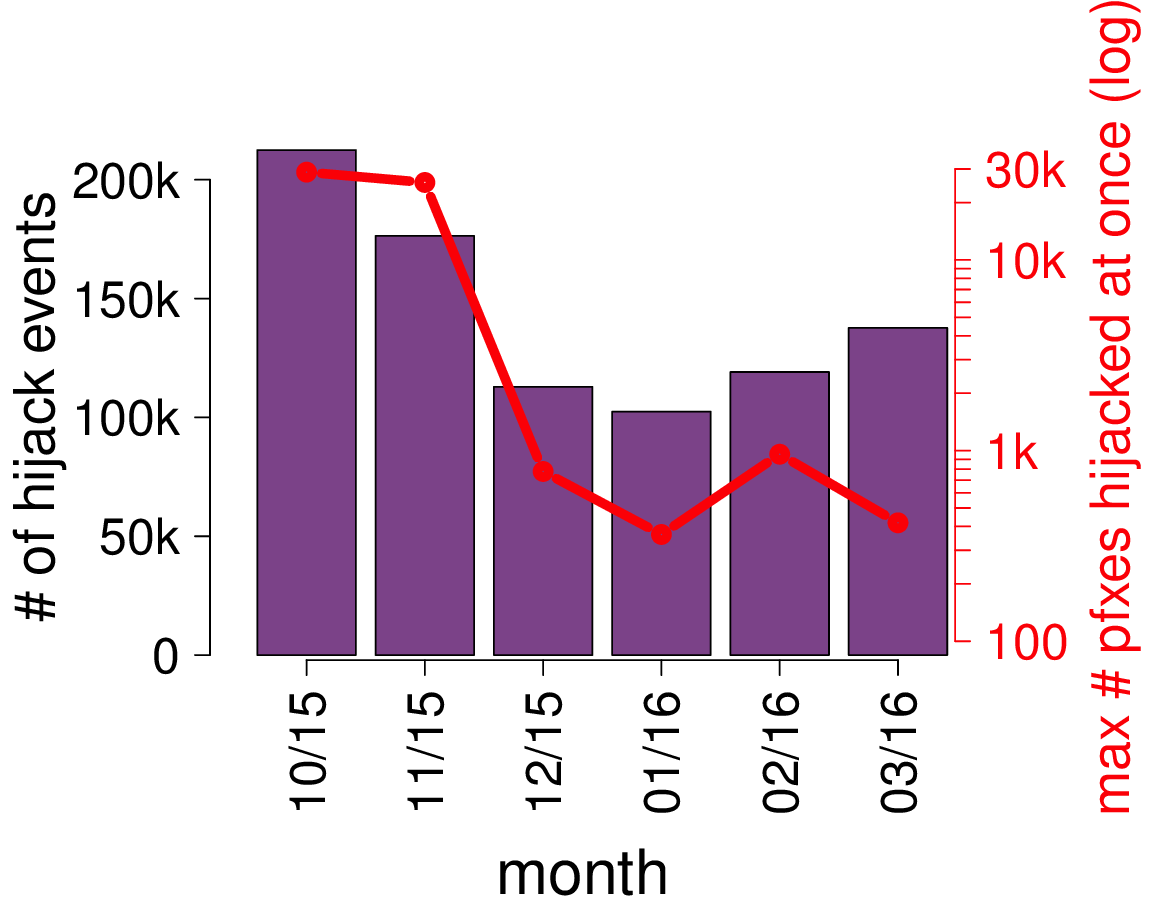
These attacks, commonly referred to as BGP hijacks , involve getting a router to falsely announce that it has a better route to some IP prefix. By hijacking all the IP prefixes pertaining to the nodes in one component, the attacker can effectively intercept all the traffic exchanged between the two components. Once on path, the attacker can sever all these connections effectively disconnecting the two components.
An animation of the attacks can be found on our website. The extreme centralization of Bitcoin from an Internet viewpoint makes partition attacks particularly effective as few IP prefixes need to be hijacked. While intercepting Bitcoin traffic using BGP hijacking is effective, any un-intercepted Bitcoin connection bridging the two components would quickly render the partition ineffective.
Due to factors such as multi-homing, some nodes cannot be prevented from exchanging information, forming some kind of persistent connections. The presence of such connections makes partitioning attacks more challenging for the attacker, but not impossible. In our paper , we elaborate on how an attacker can provably identify and mitigate these persistent rogue connections by reducing the size of the partition she is trying to achieve.
By partitioning the network, the attacker forces the creation of two parallel blockchains. Moreover, discarded transactions will be irrecoverably canceled if there exist other transactions in the prevailing branch of the chain which spent the exact same Bitcoins conflicting transactions. Bitcoin nodes are designed to request blocks from only a single peer to avoid overtaxing the network with excessive block transmissions.
The block is requested again from another peer only if the request is not answered after 20 minutes. This design decision, coupled with the fact that Bitcoin traffic is unencrypted, allows for a powerful attack in which anyone intercepting Bitcoin traffic can delay block propagation on the corresponding connections. To do so, the attacker performs simple modification to the content of the Bitcoin messages she intercepts.
As Bitcoin messages are not protected against tampering, neither the receiver nor the sender have any indication that the message has been modified, allowing the attacker to stay under the radar.
The actual impact of such an attack depends on the victim and ranges from double spending for merchant nodes to wasted computation power for miners. An animation of the attack can be found here. Illustration of how an AS-level adversary AS8 which naturally intercepts a part of the victim's traffic node C can delay the delivery of a block to it for 20 minutes.
None of these attacks lasted very long, but they were enough for the attackers to pretend to be the mining pool and tell the mining client to connect to a second server under their control. Lack of authentication in the Stratum protocol meant this happened seamlessly, and some miners didn't discover anything was amiss until weeks later.
Although the attacks stopped once the upstream provider of the Canadian ISP was notified, it is unclear whether the attack was performed by a rogue ex- employee or by an entity having obtained access to the ISP's network.
BGP hijacking isn't new, and in the recent past has, for instance, led to the routing of US Internet traffic through Belarus and Iceland. Cybercriminals' interest in bitcoins isn't new either. In another VB paper, " Well, that escalated quickly.
From penny-stealing malware to multi-million-dollar heists, a quick overview of the bitcoin bonanza in the digital era ", Kaspersky 's Santiago Pontiroli will take a look at malicious activity aroud bitcoins and other cryptocurrencies. Or, if you have some interesting last-minute research to contribute, why not submit an abstract for one of the seven remaining slots.
Tags bgp bitcoin network stratum. He shares his views on the expo and the industry. There are a number of security solutions on the market that are designed to increase the default protection provided by Office