Bitcoin wallet passphrase cracker
In these instances, we have hand-crafted highly optimized GPU software to provide huge speed advantages. The algorithms used to generate the password permutations are proprietary, but are designed to be flexible in order to handle unusual requirements.
The encryption used by the Bitcoin-core wallets is much harder to break than most encryption schemes. This is why an optimized, distributed, specialized program is required to attempt large numbers of brute force decryption attempts. We support hardware wallets such as Trezor and Ledger. We support brain wallets and BIP38 encoded wallets too.
The full list is here. Should you trust us with your wallet? If you send us your wallet, and we decrypt the password, then it would be possible for us to steal the money that the wallet holds. Fortunately, the design of the bitcoin-core wallet is such that you can send us just part of the wallet information. The part you send us allows us to decrypt the wallet, without giving us any opportunity to steal your money. See various detailed explanations on the bitcoin wallet design google them.
If the password is not found in this first try we will let you know, and provide you with the list of tried passwords. We can discuss further options. We will not charge you anything as we believe in no cure no pay. Is yours not in here? Do contact us anyway as we might have already or will work on a solution. Wallet Wizards was founded by three Dutch guys working as information security professionals and ethical hackers.
In our day-time jobs we get asked by our clients to break into to their computer systems and give advice on how to further secure. Testing the effectivity of password policies - by cracking passwords - is an essential part of our job. We have 30 years of experience combined. During these years we have seen first hand and on a very large scale how people generate passwords, people use a certain method for making rememberable passwords.
We can use that knowledge for this service. Still wondering who we are? Or do a quick google search to see the list of academic research on password cracking we have supervised. Have you got any questions about us or our approach? Before we complile John The Ripper, we need to make some changes to the configuration. Enter the following command to edit the configuration file:.
After this command, you should see the above screen. This is the instructions for how to build John The Ripper. Before we proceed, you need to be careful to only modify the following settings unless of course you know what you are doing. It's nothing like word. Think notepad but without the use of a mouse. The purple circle in the above example shows where your cursor currently is. To navigate the file, you will use the arrow keys. You will want to use the down arrow key to get to the correct line and make the below changes.
Scroll down the file using the down arrow until you get to the line that says. With version downloaded on , it is line Simply remove the pound symbol in front of the line so it reads - to do this, simply place your cursor on the pound symbol and press the delete key once.
We now need to save and close the configuration file. You should now be returned to the terminal prompt. If successful, you will have something like the image above. The area in the purple square shows a successful test of John The Ripper. It was able to process Like I said, it's a very slow process. The inital test however only used one CPU core so if you have multiple cores, you can multiply the text number by core count.
Also remember, depending on the speed of the computer on which the wallet was originally encrypted, the faster or slower the decryption process. John The Ripper is extremely configurable. In this guide, we are going to look at just the basics to get you going.
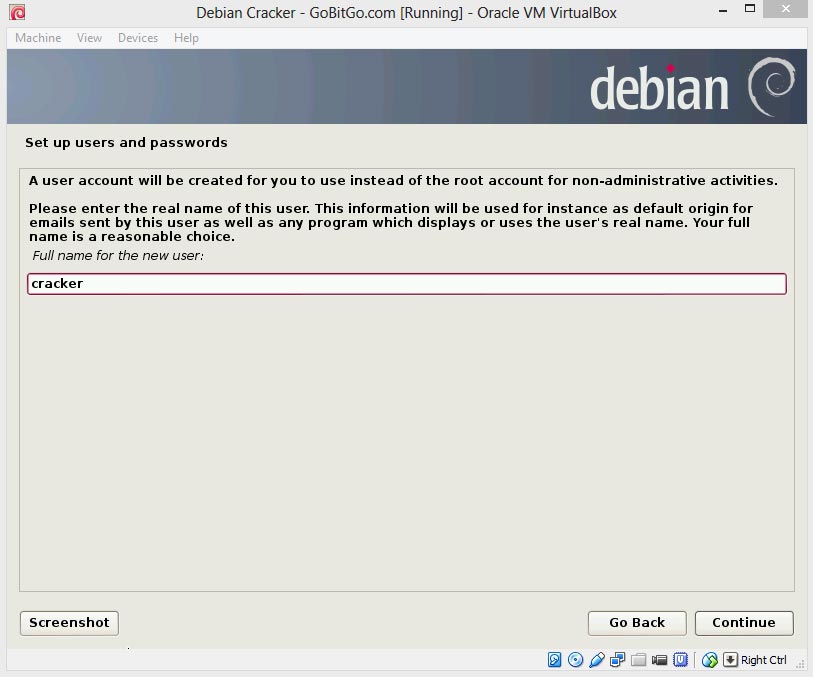
In the list below, every location that says "cracker" is the usernamed used in the inital setup part 2. If you used a different username to setup Debian, replace that name with cracker. Let's break this down before we continue.
In the above line, we are calling John The Ripper and giving four options to utilize. Please also notice the space between each option. While John The Ripper is running, press the "q" key. It will shut down but can be resumed at a later date. While writing this article, I forgot my new bitcoin wallet address - luckily there are no coins in it but it's a great example for you to test with. I thought my password was GoBitGo but it's not. I likely mistyped a character. Can you crack the password?
This test cracking is an important step. It will confrim that your virtual environment is properly working and has the ability to potentially crack your password. To test this process, you will need a copy of the encrypted wallet and a word list that I generated to find the password.
The wordlist is , passwords long but fear not, the correct answer is between line 25, and 30, which should not take too long to find - even with one CPU core. This list was created using a double replace method and has over 2,, passwords.
I cut it into a quater to make it a smaller download. The below guide will use the files from above to test John The Ripper. When you are ready to crack your own wallet, simply replace the files from this guide with your own.
The decryption program does not care about your wallet file - what it does care about is your wallet's private key. There are multiple ways to extract the private key but for this example, we will ask John The Ripper to do so.
If you choose to do so another way, you can skip the following step and just place it in an empty document on the virtual environment. We now need to get the required files into the virtual environment. In previous steps, we setup the environment with "Guest Additions" which allow us to drag and drop files directly into the virtual environment tas well as supporting copy and paste.
Unfortunately, you can not just drag and drop files directly onto the virtual environment desktop well, you can but you will have to change some settings of Gnome - this is the Linux GUI.
We will need to open the File Manager. This will open the file manager. You can then drag and drop your files directly into this file manager. Please also make sure you are in the home folder inside the file manager. In the image above, the folder location is in the blue square.
If you are not under the home directory, click on "Home" on the left side of the file manager. If for some reason you could not drag and drop your files into the file manager and Guest Additions are not working, I would suggest either:. Now that we have the requried files on the virtual environment, we are ready to extract the private key from your wallet file.
To do so, in the terminal, enter. Your wallet key will be saved in the file named wallet hash. If you want to verify this has worked, you can open this file by entering.
It will display the following from the test wallet - your personal wallet will have a different hash. Please enter your desired amount but it can not be more than the amount of cores you have on your computer.
If everything works, you will see the above image. Now, it's time to be patient. If you want to check the status, make sure you have the terminal as the active running application just click on it and press any key.
You will then be given the information of each CPU core - how fast, how far through the list and current active line from the wordlist. In the above example, you can see we are running 4 CPU cores and the cores are ranging from When John The Ripper finds the password, it will show it.
Above is an example with the found password - I placed it in the purple box for you to see. There you have it! Even after it finds the password, the program will keep running on the other cores until it comes to the same conclusion. Some of you will notice that other CPU cores will find the password as well and you may be thinking that the program is overlapping on each core but the timing does not work out to that conclusion.
What I believe is happening is once the password is found on a core, that core shuts down but the program does not update that the specific line as checked.
It's likely a programming bug but should not interfere with the process. This is possibly the most important step! Unfortuntely, this is not a one size fits all solution. When we look at password decryption, we ask for the most likley to least likey password canidate and they are often very similar but not close enough for a universal solution.
I often find myself creating a custom program creating a unique list of potential passwords to first try. With that said, the below program can very well find your password if it was a simple typing error.
The program was not created by GoBitGo but rather I found it online here. It has been modified to create a list of potential passwords and place them in a file ready for John The Ripper. S Dollars, Bitcoins or Litecoins. We will generate your password list usually within 72 hours. If you later hire us to decrypt your password, and we are successful, this amount will be credited back to you. Email us at info gobitgo. To use this program, first you will need to download it via the above link WordListGenerator.
Once downloaded, place it in your virtual terminals file managers Home folder. It's the same instructions as to section 6. You will now need to enter what you thought your pass phrase s is. Once uploaded, go to your terminal and enter. This is the list of what you thought the password could be.
You can enter any amount of possibilities here. The formatting needs to however stay the same. Each potential password needs to placed in apostrophes with a comma separating each possibility and no comma at the end. But what if you think your password may contain an apostrophe? Simply add a back slash behind it. Here is an example of a single potential password and it contains an apostrophe:. To run the program:.
If you got this far, you've already executed a cracking command. All you need to do is follow step 5 again, except this time, you are not going to upload a wordlist file since you created one on the server. Step 2 - Change your wallet passphrase.